By Paul Ducklin, Principal Research Scientist at Sophos
Our cybersecurity antennae always start vibrating when we see warnings about attacks that involve a new type of file. We’re sure you have the same sort of reaction.
After all, if a file type that you’ve treated for years as mostly harmless suddenly turns out to be possibly very dangerous, you’re faced with a double dilemma:
- How long will it take to unlearn an ingrained habit of trusting those files?
- How long will the crooks take to start abusing this new-found knowledge?
We’re all aware of the risks posed by unknown EXE files, for example, because EXE is the extension for native Windows programs – even the operating system itself is implemented as a collection of EXEs.
Most of us also know to be wary of DLLs, which are actually just a special type of EXE file with a different extension to denote that they’re usually used in combination with other programs, rather than loaded on their own.
We’ve learned to be wary of DOCs and DOCXs and all the other Office filetypes, too, because they can include embedded programs called macros.
We’re also aware of a range of risky script files such as JS (for JavaScript), VBS (Visual Basic Script), PS1 (Powershell) and many others that are plain old text files to the untrained eye, but are treated as a series of system commands when processed by Windows itself.
We’ve even taught ourselves to be wary of the extent to which Windows itself misleads us because of its default approach to filenames – as in the case of the files alert and alert.txt below, which go out of their way to convince us they’re just innocent text:
Forget what they look like: those old-school icons on the left that give the impression of being medieval scrolls don’t denote plain old written text at all.
Ironically, however, the icon in the middle that looks like a crisply modern digital document, and that goes with a file that’s actually called document, really is a text file. By default, Windows suppresses filename extensions, which are the all-important characters that follow the last dot in a filename, such as the .docx at the end of the Word file TaxReturn.docx or the .exe at the end of the program Notepad.exe.
Annoyingly, Windows itself very often uses extensions to decide what to do when you click on a file – for example, whether to view it harmlessly or to execute it riskily.
Yet the operating system rather patronisingly assumes that you don’t need to bother yourself with those pesky extra letters at the end of your filenames.
Indeed, if we turn on the View > File name extensions option (highly recommended!) in File Explorer, you’ll see the dangerous truth behind those “scroll icon” files that looked above as though they were called alert and alert.txt:
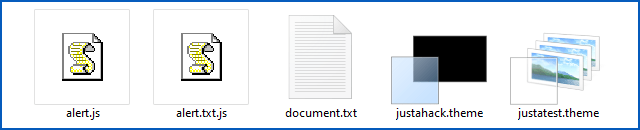 In real life, those are .js files, and if you double click on them thinking you are about to open them up to view their contents, then you will get an unpleasant surprise. Windows will automatically run them as all-powerful JavaScript programs – not in the comparative safety of your web browser, but directly on your computer as local apps.
In real life, those are .js files, and if you double click on them thinking you are about to open them up to view their contents, then you will get an unpleasant surprise. Windows will automatically run them as all-powerful JavaScript programs – not in the comparative safety of your web browser, but directly on your computer as local apps.
(Apparently that icon doesn’t represent a scroll. It’s meant to be a script. Who knew?)
Enter the Theme file
At right hand side of the images above, you’ll see files with the extension .theme, denoted by icons that depict what look like a series of background images. We’re willing to bet that if you’ve ever downloaded and used .theme files (or .themepack files, which are just a collection of .theme files bundled together), you’ve not worried too much about security. Very loosely speaking, Windows Themes are just INI-style text files that specify various settings for background colours, wallpapers, and visual effects.
Here’s a simple example, a copy of the file justatest.theme depicted above:
(No, we don’t know what the text MTSM=DABJDKT in the last line means or what it’s for; we just know that Microsoft insists that you have it in the file and says, “You do not have a choice of values for this parameter.”)
Admittedly, just loading untrusted image files, such as the Wallpaper file specified above, can theoretically be dangerous.
That’s assuming there’s an unpatched vulnerability in one of your apps, or in Windows itself, that can be reliably exploited to trick your computer into running a fragment of executable code when a deliberately crafted image file is opened.
In practice, however, that type of vulnerability is rare these days – those that are found are either quickly patched or jealously guarded, and can usually be triggered by delivering a booby-trapped image directly to your computer in a web page or an email rather than relying on a Theme file to reference them indirectly.
The danger posed by booby-trapped Themes is therefore both small and manageable – giving .theme files a justifiable assessment of mostly harmless.
Despite their generally low direct risk, .theme files nevertheless received a public airing in in the notorious “Vault 7” data dump back in 2017, when WikiLeaks exposed a massive trove of confidential documents allegedly stolen from the CIA. Vault 7 included a knowledgebase article, supposedly from the CIA’s Information Operations Centre, remarking that Themes might be handy as a way of amplifying the effect of an existing exploit by allowing multiple variants of the exploit to be delivered in one go: “[I]n the cases where your execution vector uses icon rendering/file previews to exploit (link files, font files), a theme file can allow you to point to up to three other files and render them from one.”
Harmful after all
But some recent digging by a security researcher going by @bohops revealed that Themes are open to abuse by cybercrimals after all – albeit in an indirect way to phish for passwords rather than directly to implant malware on your computer.
Traditionally, .theme files are used simply as a way of triggering the automatic installation and rendering of one or more local files – indeed, that’s how the CIA envisaged using them for activating exploits:
In the animation above, you can see how double-clicking a .theme file launches the Windows Settings app, automatically navigates to the Preferences > Themes section, and then opens, copies, selects and renders the new wallpaper file justatest.png onto our desktop.
What if?
So far, things haven’t been very worrying. Bohops, however, put his “What if?” cybersecurity research hat on, and wondered what might happen if he used a Theme file to reference images out on the internet, using web URLs instead of regular filenames.
All we’ve changed is the DisplayName of the Theme itself and the “filename” specified on the Wallpaper line.
In our real-world tests, we used a genuine domain name pointing at a test server of our own, fitted out with a genuine HTTPS certificate from Let’s Encrypt.
Here, however, we have redacted the site name and replaced it with a special use domain name, as detailed in RFC 2606 and RFC 6761. We urge you to follow these RFCs in your own cybersecurity articles and documentation.
By sticking to IP numbers and domain names that are realistic but will never be allocated in real life, you avoid the risk that someone might blindly copy and paste your examples into one of their own tests and subject some innocent third party to an inadvertent, annoying and possibly even dangerous attack.
Bohops realised that the Settings app will honour the URL in the Theme file, automatically connecting to it without showing you any sort of browser window, and attempting to fetch the file that’s referenced.
That’s slightly more worrying that reading a file that’s already on your computer, but probably still not enough to reclassify Themes as much worse than mostly harmless.
In theory, getting Windows to connect to a WebDAV resource that requires authentication ought to provoke a Windows-style network login popup, using Windows NTLM (native) authentication rather than the less convincing HTTP-style credential popup that we saw above.
Nevertheless, cybercriminals might be able to recover a poorly-chosen password if they have plenty of computer power to throw at the cracking task (which can be done offline).
What to do?
Here are our six tips to stay safe:
- Read password prompts carefully. We agree with @bohops that the phishing popup we demonstrated above is more believable than seeing the same sort of login prompt directly in your browser, not least because the password box is convincingly headlined Settings. Nevertheless, the dialog does make it clear that the password request comes from a remote website, not from Windows, and that the login message comes from the site too, not from the operating system.
- Avoid opening files you aren’t familiar with. It’s harder to spot that something unusual is going on if you aren’t familiar with what is usual.
- Turn on the option to show file extensions. In File Explorer, click on the View item in the menu bar and then turn on the option File name extensions. If the Explorer window is narrow you may need to open the Show/hide tab first. Windows uses file extensions to decide how to handle files, and you should too, because the crooks love to use names like safe.txt.js or harmless.document.exe to throw you off the scent.
 Turning on the Windows option to show file extensions.
Turning on the Windows option to show file extensions.
- Use a cybersecurity product that includes outbound web filtering. Sophos products, for example, don’t just scan incoming files for malware. After all, phishing attacks don’t rely on getting bad stuff into your network on purpose – they rely on you inadvertently letting good stuff out by mistake. Web filtering can keep you clear of rogue sites in the first place to keep you even further out of harm’s way.
- Pick proper passwords. No, a complex password wouldn’t protect you against the HTTP Basic authentication trick shown above if you entered your own password anyway. But proper password choice will protect you if all an attacker can acquire is a strongly hashed version of your password, because the only way to recover the password is to try a lengthy list of likely password in the hope of finding one that matches the hash. Don’t be the first to fall!
- Report unusual or suspicious content promptly to your security team. We’re betting that you’ve never, or at most very rarely, had anyone trying to foist a Theme file on you before. If an outsider tries to talk you into clicking, opening or approving something that you didn’t expect, don’t need and that you can’t see the point of… ask yourself, “Why would anyone do that?”